Attack Vectors
Prevent Account Takeover with Perception Point
Account takeover (ATO) – whether the target is your business email or your company’s bank accounts – are on the rise. Sophisticated attackers understand that once they gain one of your employees’ credentials they can “land and expand,” causing unprecedented damage.
Perception Point’s solution enables complete protection for Account Takeover – preventing attackers from infiltrating the organization, detecting anomalies that could suggest an account has been compromised, stopping attackers from spreading malicious content onto other users, and providing incident management, remediation and reporting.
The ATO Challenge
Today, once attackers get a foot in the door and obtain credentials for authenticated access to your mailbox or other cloud applications, they can do whatever they like – spread malware, deliver malicious links and even obtain personal data or exfiltrate funds.
The complexity of an account takeover is that in most cases, there are no preliminary signs for the user. They don’t know their credentials have been compromised, their inbox looks the same, and there is no sign for suspicious behavior, until the day when the attacker decides to go ahead with their ATO-based attack, and it’s too late to stop the attack.
The Account Takeover Kill Chain
Step 1
Credential Theft
Intruder obtains legitimate log-in credentials of the targeted account via phishing, social
engineering, third-party breaches, or malware.

Step 2
Establish Control
The attacker establishes control of the account by implementing measures that will leave him unnoticed for the required period of time.
Step 3
Reconnaissance and Weaponization
Intruder explores the account to understand how the compromised account can be exploited and look for an opportunity to strike.
Step 4
Delivery
The intruder will either deliver his attack via the compromised account or seek to expand in the organization, spreading files or URLs until another user takes the bait.
Step 5
Result
The intruder obtains confidential data or exfiltrate funds from wrongful actions of the compromised users.
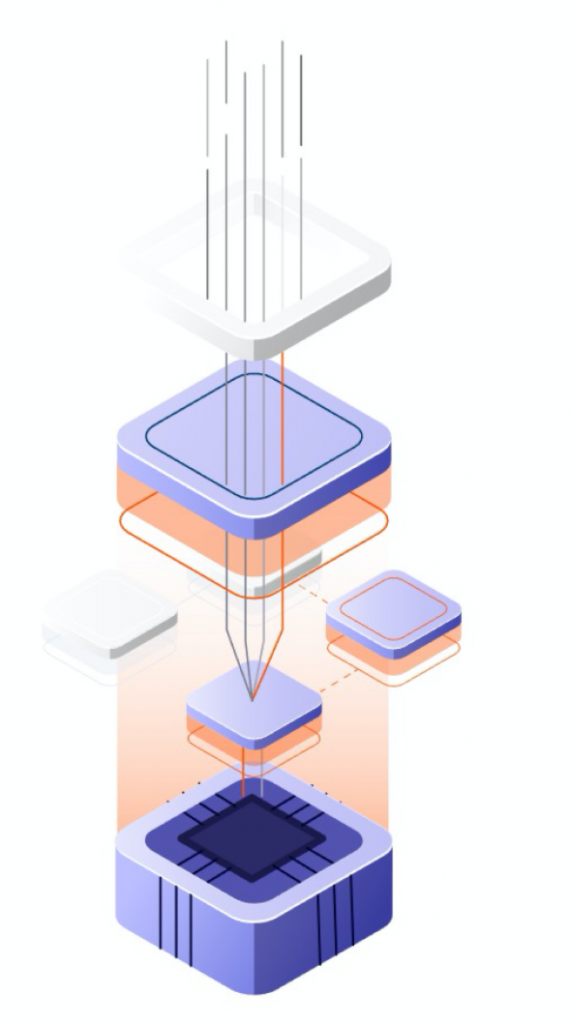
Multi-Layered Approach Throughout the Kill Chain for Account Takeover Prevention
Perception Point’s different engines work together to intercept any account takeover attempt, at any stage, preventing, detecting, and remediating. Here’s how.

Stop Employee Credential Theft
Designated, unique engines work to prevent any attempt to phish credentials from each channel protected by Perception Point.

Monitor Anomalies for Compromised Accounts
Stop Attackers from Landing and Expanding
Stopping attackers from spreading malicious content onto other users, in lateral phishing attempts.

Instantly Detect & Remediate Compromised Accounts
Incident management and reporting service streamlines the remediation & containment of every account takeover attempt.
Our Advantages
Complete Advanced Threat Detection
Maximum
Usability
Providing ultimate detection without compromising on content functionality, allowing your employees to collaborate and create together safely.
Enhanced Line of Defense
Creating an additional obstacle in the way of sophisticated attackers from gaining financial benefits. Internal email scanning enhances your overall network protection as it identifies threats even if they passed the first lines of defense of other entry points.
Business‑supporting Speed
Scanning external and internal emails without causing critical delays to your ongoing operations, effectively encouraging users to share content is protected channels, such as email (vs. private apps for example), and providing your security full visibility and control.
Unlimited
Scale
Whether your employees share huge files or multiple URLs – Perception Point will scan it. Cloud-native approach allows the platform to support any amount of data, on every single moment.
Deployment
Ready
Like our Advanced Email Security solution, the Advanced Internal Email Security product is deployed in one-click, creating zero fuss to you and your IT team.























