In this blog post, we review one of the recent malware examples that has resurfaced.
First observed in 2016, Revenge RAT is a malware that is classified as a Remote Access Trojan. This means that threat actors usually use it to remotely control infected PCs, surveil users by capturing keystrokes, watching them via webcam, or even listening to their microphones.
Through Revenge RAT malware, threat actors can remotely execute malicious tasks on the user’s computer and steal any sensitive data available to them.
The Revenge RAT Malware Phishing Email
Like almost every other attack these days, Revenge RAT malware is delivered via email, the number one attack vector for cyberattacks.
The user receives an email that appears to be an urgent invoice request. The email instructs the user to open up the attached invoice, an Excel file, and enable both editing and content, in order to “view” the content of the invoice. In reality, enabling editing and content activates the attack chain flow, which we will explore further later on in this post.
It is important to note that there are some obvious warning signs within the email:
- The email subject is the exact name of the attached file, which indicates a low effort attempt by the threat actor to manipulate the user or convince them that the invoice is real.
- The email contains an explanation of how to open the document, which usually indicates that the threat actor is employing a social engineering technique by trying to get the user to perform the exact commands required to execute the malware.

The Revenge RAT Malware Attack Flow
The components of the Revenge RAT malware attack occur throughout multiple stages. The image below shows the steps involved in the attack:
Step 1: First, the XLS file (“QuickBooks Invoice Enclosed 10001144747631.xls”) is used in the attack vector by executing the macros it contains to run mshta.exe on a file located on the C2 server.
Step 2: Then, “Enc.txt” (the executed file) executes another file on the C2 server using PowerShell.
Step 3: Next, the executed file (“Server.txt”) creates a folder located on the user’s computer; inside, 4 files are created as the file starts execution of one of the its new files.
Step 4: The first file executed (“IICOZODNLSRPOHUBAJWZFK.ps1”) creates a task that will run on the user’s computer every 3 minutes and will execute “IICOZODNLSRPOHUBAJWZFK.vbs”. This command contains code to execute “IICOZODNLSRPOHUBAJWZFK.hta” that will then execute “YHZYJGKGYAFXQEZFSRCPPY.ps1” (containing obfuscated Revenge RAT malware).
Step 5: Upon the execution of “YHZYJGKGYAFXQEZFSRCPPY.ps1”, two files within the file are used to run the Revenge RAT malware.
Step 6: The Revenge RAT malware communicates with the C2 server and the threat actor obtains a new C&C computer for his collection.
Below we provide a detailed analysis of files and commands used during the various stages of the Revenge RAT malware attack.
Initial Access
The initial document, “QuickBooks Invoice Enclosed 10001144747631.xls”, contains macros. The creator of the document sets these commands to perform an action or a set of actions within the Excel document.
In the email, the threat actor explains that in order to view the content of the document the user must enable editing and enable content. Included in the document are two warning signs that there may be macros.
Opening up the document, the user sees a clean Excel sheet and must click on “Enable Editing” and “Enable Content.” Once clicked, the malicious macro code begins to work.
The macro code is obfuscated within other text, making it difficult for most users to understand:
Three replace functions act to replace embedded strings within the “WHBKJDFVRUXXYRDLFLHVGG” variable. The program then runs the content of the variable by triggering the “Create” method under the Win32_Process class (WMI class represents a process on an operating system).
The de-obfuscated string looks like this:
The macros execute “Mshta.exe”, which is a known signed Microsoft program. It can proxy execution of malware (execute HTML applications files) and establish a connection with the C2 server in order to download a file named “Enc.txt” (which is an additional payload for the attack chain).
Enc.txt is yet another obfuscated file; it contains a script tag which will be executed through mshta.exe:
The script is written in Visual Basic, which we know because there is a “language” indicator in the opening tag. By the end of the script, it executes a PowerShell command, which downloads another file from the C2 server and executes its content.
Below are the variables (and their values) of the PowerShell command:
- AHJTRRXVBYENECJTZIBQCT: StreamReader Class Object
- ARYSWDUYBLHGDITSWDFEOG: WebRequest Class Object
- TESIORILDCDTLCYOWDHSGO: Create, (invoked from WebRequest) creates web request to the other file located on the C2 server
- KGHJKOKAPLPTBRQZIRBJZS: GetResponse
- BKCOKSGBGDNXDEAXSBNVJU: GetResponseStream
- ZUVEOIPLZEGADWFECARLXA: ReadToEnd
Defense Evasion
In order to evade defense measures, the Revenge RAT malware contains “Server.txt”, which is an obfuscated PowerShell file containing several variables. These variables represent four malicious files that are created on the user’s computer.
The file starts its execution by checking if the folder it wants to create already exists. If it doesn’t, then it creates the folder.
The Malware Kill Chain Process
Below is explanation of what each file does during the Revenge RAT malware kill chain process:
C&C Server Connection
As previously mentioned, the command executes the Revenge RAT malware. We managed to extract the executable file from the obfuscated PowerShell file to provide a better overview of the payload.
The screenshot below shows basic information of the payload executable:
We can see that the code is actually compiled with .NET, meaning we can open the executable in DnSpy and view the code. Surprisingly, this malware’s code is readable and not obfuscated.
One of the functions present in the code is “Config”, which contains the configuration of the RAT:
Revenge RAT malware Config Class
Below are the members of the config class and their functionality:
- Host: C&C Server
- Port: C&C Port
- ID: Unique ID of the installed RAT
- Key: Magic string used as a separator to split data on the packets
- CurrentMutex: Mutex placed by the RAT on the system
- Splitter: Magic string used as packet end string
- Stopwatch(): Member function used to reset stopwatch
From computer to C2 server
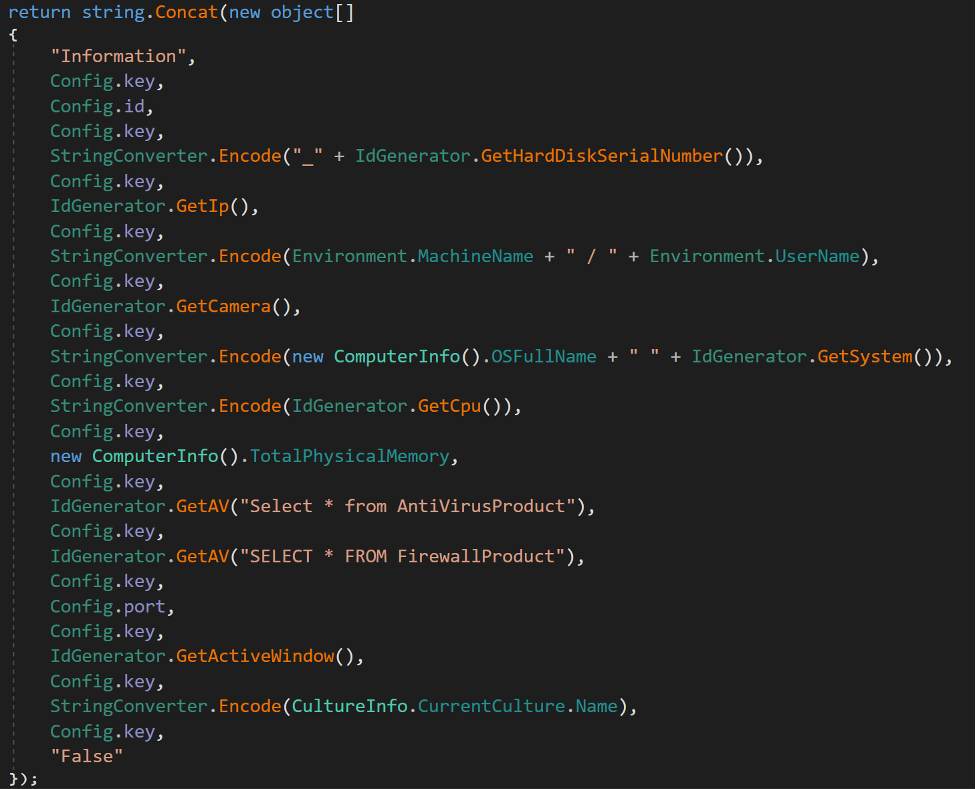
The first packet sent from the user’s computer to the C2 server contains lots of sensitive data related to the user’s computer. The data collected using a custom class presents the code named “IdGenerator”. Below are some of the methods the class uses to retrieve sensitive data:
- GetHardDiskSerialNumber: Get hard disk serial number
- GetIp: Get IP address
- GetCamera: Get information about the camera
- GetSystem: Get processor information
- GetCpu: Get CPU information
- GetAV: Get the antiviruses installed on the system
- GetActiveWindow: Get active window or window of the application used by the user
This packet contains everything the RAT malware collected using the function we explained above. Now, when the malware establishes its connection, it can send commands that the user’s malware agent will handle.
C&C Commands Execution
One of the classes within the code is called “PacketHandler”; it contains a function called “Handler”. “Handler” is in charge of handling all received C&C commands. The C2 server can send 5 commands to the user’s computer:
- PNC: Ping/Heartbeat command, which makes sure the connection is still alive.
- P: Sends the name of the current working window on the user’s computer.
- IE: Checks for installed plugin in the registry of the user’s computer under “HKCU\Software\”
- LP: If the plugin in IE command isn’t found, the malware creates a new registry key under “HKCU\Software\” named after the RAT mutex (base64 encoded) with a subkey, named after the value inside of it (MD5 hashed) and the value of the subkey. This becomes a dll file sent on this command in order to maintain persistence and for further execution.
Recommendations
Revenge RAT malware causes a massive problems when deployed on a highly valued employee’s computer. Most likely delivered via a phishing email, it targets the individual person. It also requires the user’s attention to run the macros in order to initiate the attack.
To avoid falling victim to this type of attack, we recommend the following steps to mitigate your organization’s risk:
1. Educate your employees on the need for email security and the risk of opening suspicious emails and attachments.
2. Run email security drills every few months, to ensure that employees know what to look for in a suspicious email.
3. Create a process for employees to follow when they receive a suspicious email or link.
4. Disable macros in Microsoft Office applications.
For more information about how to protect your organization against malware attacks delivered via phishing emails, read our Advanced Email Security guide today.
Here’s some related content you may enjoy: How to Prevent Malware Attacks
IOCs
IP Address:
45.147.230.231:2222
URLs:
hxxp[://]45[.]147[.]230[.]231/a/Enc[.]txt
hxxp[://]45[.]147[.]230[.]231/a/Server[.]txt
Samples SHA-256:
Client.exe – f6b2c58f9846adcb295edd3c8a5beaec31fff3bc98f6503d04e95be3f9f072e8
Lime.dll – 9fca9b70d87c1b81bbb48209986e59d9cf92ab3f5bfd5fecf432caf0c3fed444
YHZYJGKGYAFXQEZFSRCPPY.ps1 – 37a94b72cec528ffaa6fb82559ba2dc0b82bc1270edc85e7cee98d16f6b9c242























