Cybersecurity
for the Modern Workspace
Selected Customers














Protect More. Manage less.
Powered by AI.
Empowered by People.
Your users’ workspace has already changed. Email, collaboration and productivity tools are in the cloud, accessed from any browser, everywhere. While your employees are more exposed than ever, your security team is stretched thin and overloaded. It’s time to go beyond traditional point solutions.
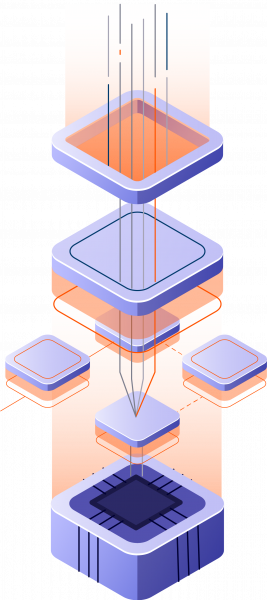
Perception Point uniquely combines an AI-powered threat prevention platform, leveraging LLMs, image recognition, and anti-evasion technology, with a 24/7 managed incident response service.
Threat actors use GenAI and human expertise to breach organizations – we use them to protect yours.
STOP ANY THREAT
Threats have evolved. Stay ahead of the attackers.
Prevent the most sophisticated and evasive cyber attacks from ever reaching your organization. AI-powered detection technology, scale-agnostic patented dynamic scanning, and multi-layered architecture block all social-engineering attempts, file & URL-based threats, malicious insiders, and data leaks.
MANAGE WITH EASE
Your security team is overloaded. Let us do the
heavy lifting.
Reduce resource spend and time needed to secure your users email and workspace apps. Our all-included 24/7 Incident Response service, powered by AI and cybersecurity experts, manages our platform for you. No need to optimize detection, hunt for new threats, remediate incidents, or handle user requests. We do it for you — in record time.
POWER USER PRODUCTIVITY
Securing the workspace is complex. Consolidate and simplify.
Protect your user’s top attack vectors including email, enterprise browsers, Microsoft 365 and Google Workspace collaboration apps, CRMs, and storage solutions with a unified platform. Deployed within minutes with no changes to your native infrastructure, zero IT fuss and a frictionless end user experience, you gain centralized control and detection synergy from one intuitive console.
See Perception Point in action!
100%
Dynamic Scanning
Dynamically scan 100% of email traffic including embedded files & URLs regardless of the volume.
99.95%
Detection Rate
Catch any threat type including evasive malware, social engineering attacks and ATO attempts with unprecedented accuracy.
75%
SOC Time-Saving
Save up to 75% of SOC time with a natively integrated, managed Incident Response service managing incidents and remediating threats.
Testimonials





TALK TO SALES
Ready to Try
Perception Point?
News & Press.


Awards